Teck Digital Systems Cyber Security team works to protect our corporate and operational systems from internal and external risks such as virus attacks, network outages and costly repairs. By working in partnership with these experts and following best practices in cyber safety, you can help keep Teck’s networks secure.
Lock It Before You Leave It
Take a moment to think about the information you have direct access to via your Teck computer. Consider the people outside of your team and outside of Teck who should not have access to this information, and the risks associated with unauthorized access to your computer.
Even the best cyber security solutions cannot stop someone from initiating an attack from your computer when it’s left unlocked, so always remember to lock your computer when you’re not using it.
Improve Password Security
Strong passwords help mitigate the risk of a cyber attack against you and against Teck. The most effective passwords are:
- Unique: Never use the same password twice.
- Long: Try a pass phrase, one that is easy to remember and hard to crack.
- Secure: Never write down or share your passwords; use a password management application, such as LastPass, which is Teck supported and can securely store and manage your passwords for you. LastPass can be requested via the Teck Service Portal.
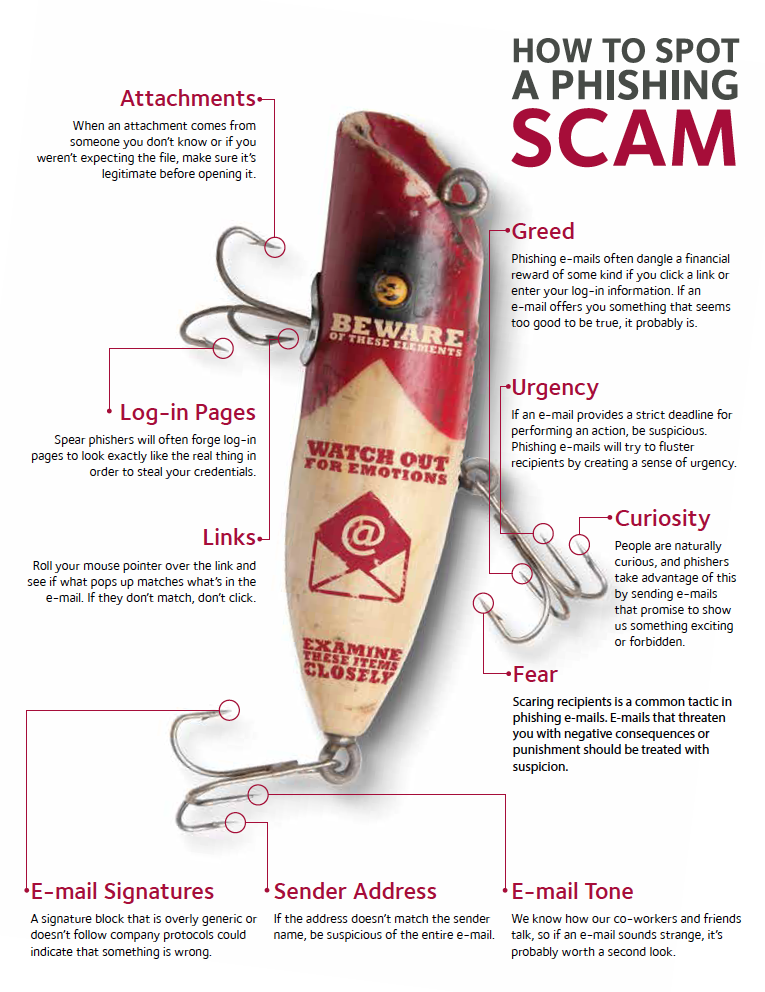
Catching Phish
Phishing is a type of cyber attack that uses email or a messaging service to trick you into taking an action, such as clicking on a link or opening an email attachment that will download a malicious program or give the sender access to your computer.
If you receive an email that you think might be suspicious, click the Report Phishing button on your Outlook toolbar, or, forward the original email from a mobile or other device to phishing@teck.com. The email will automatically be forwarded to the Cyber Security Incident Response Team, who will review it for any suspicious activity and let you know if it’s safe.

.png)

